what is azure
Microsoft Azure for Sysadmins and Security Professionals
Microsoft Azure for Sysadmins and Security Professionals: A Deep Dive
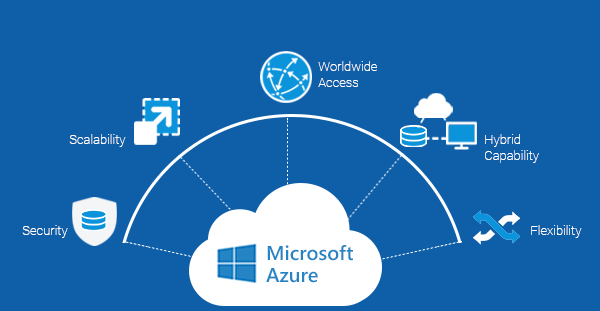
Cloud adoption has transformed the way sysadmins, security analysts, and network engineers operate. Among the cloud providers, Microsoft Azure holds a unique spot—especially for those working with Active Directory, hybrid environments, cybersecurity, and enterprise networking.
In this post, we’ll explore how Azure fits into a modern technical stack, with a focus on security, networking, and system administration use cases. Whether you’re defending infrastructure, deploying secure networks, or running a lab to test attacks, Azure has tools worth knowing.
🔐 Azure and Cybersecurity: A Defender’s Playground
Security is deeply embedded in Azure’s ecosystem. Microsoft has invested heavily in making Azure not just compliant, but proactive in threat defense.
🔸 Key Security Features
- Microsoft Defender for Cloud: Security posture management and threat detection.
- Microsoft Sentinel: A cloud-native SIEM/SOAR with built-in threat intelligence.
- Role-Based Access Control (RBAC) and Conditional Access: To enforce least privilege and MFA.
🔹 Sample KQL Query: Detecting Password Spray Attempts
SigninLogs
| where ResultType == 50053 or ResultType == 50034
| summarize Attempts=count() by IPAddress, UserPrincipalName, bin(TimeGenerated, 1h)
| where Attempts > 10
🔹 Azure CLI: Enable Defender for Cloud
1
az security auto-provisioning-setting update --name default --auto-provision "On"
🌐 Networking in Azure: Beyond Subnets and VNets
Azure networking looks familiar to traditional network engineers—VNets, subnets, routing tables—but with cloud-native power.
🔸 Core Tools
- NSGs (Network Security Groups): Firewall-like rules at subnet/NIC level.
- Private Endpoints: Access services privately without public IPs.
- Azure Firewall: Stateful L3-L7 inspection.
🔹 Azure CLI: Create a VNet and Subnet
1
2
3
4
az network vnet create \
--name MyVNet \
--resource-group MyResourceGroup \
--subnet-name MySubnet
🔹 Azure CLI: View NSG Rules
1
az network nsg rule list --resource-group MyResourceGroup --nsg-name MyNSG
🧑💼 Sysadmin Use Cases: Azure + Active Directory
Azure is a natural fit for Windows sysadmins, especially those working with Active Directory.
🔸 Core Components
- Azure AD (AAD): Cloud-based identity platform.
- AAD Domain Services: Offers Kerberos, LDAP, and NTLM in the cloud.
- Azure AD Connect: Sync on-prem AD to Azure AD for hybrid identity.
🔹 PowerShell: List All Azure AD Users
1
2
Connect-AzureAD
Get-AzureADUser -All $true | Select DisplayName, UserPrincipalName
🔹 PowerShell: List Directory Role Members (e.g., Global Admins)
1
2
$role = Get-AzureADDirectoryRole | Where-Object {$_.DisplayName -eq "Company Administrator"}
Get-AzureADDirectoryRoleMember -ObjectId $role.ObjectId
🛠️ CTF Labs & Blue Team Exercises in Azure
Azure is great for spinning up attack/defense labs or practicing incident response in a live environment.
🔸 Lab Ideas
- Build an Active Directory lab with 1 DC and 2 clients
- Install Sysmon + Azure Monitor Agent to forward logs
- Set up honeypots and watch for brute force in Sentinel
🔹 Sample Sysmon Detection in Sentinel (Process Injection)
SecurityEvent
| where EventID == 4688
| where CommandLine contains "rundll32" or CommandLine contains "regsvr32"
| summarize count() by Account, CommandLine, bin(TimeGenerated, 1h)
⚙️ Final Thoughts: Azure as a Technical Swiss Army Knife
For sysadmins, network engineers, and security pros, Azure is more than a cloud provider—it’s a lab, a production-grade infrastructure, and a security operations platform all in one.
By understanding Azure’s capabilities through a technical and security lens, you expand your toolkit and future-proof your skill set in a world where hybrid cloud is the default.
🔎 Coming Soon on the Blog
- Building an Azure AD Attack Lab for Red Team Training
- Writing Sentinel Analytics Rules to Detect Lateral Movement
- Securing Hybrid Azure AD with Conditional Access Policies
- Enumerating Azure AD Permissions Like a Pentester
1
2
Would you like this exported to a `.md` file, or posted in a specific CMS format (e.g., WordPress or Jekyll front matter)? I can also help generate YAML metadata if you need it.